In partnership with

PatchDay Alert: 2026-05-07

|
|
DAILY BRIEF · MAY 7, 2026
|
|
Five patches today, two that need your attention right now. Gotenberg has a CVSS 9.4 SSRF bug that lets unauthenticated attackers bypass its deny-list and hit your internal services, including cloud metadata endpoints. Right behind it, Apache HTTP Server has a double-free in mod_http2 (CVSS 8.8) that could hand an attacker remote code execution on any internet-facing instance.
|
|
TOP THREAT TODAY
|
|
An attacker can crash your Bandit-based Elixir/Erlang web server by sending crafted WebSocket continuation frames that pile up in memory without limit. No authentication needed. The server just keeps buffering until it runs out of RAM and dies.
Who's affected: Elixir developers and operators running Bandit as their HTTP server with WebSocket endpoints exposed to the internet
| |
Patch this week.
Upgrade the Bandit dependency to the patched version listed in the advisory and redeploy your application.
|
NVD
Ref 1
Ref 2
|
|
|
CVE-2026-23918
CVSS 8.8
EPSS 0.06%
|
HIGH
|
A double-free bug in Apache HTTP Server's HTTP/2 handling can be triggered when a client sends an early stream reset. This could lead to remote code execution. No authentication is required, and any internet-facing Apache instance with mod_http2 enabled is a target.
Affects: Anyone running Apache httpd 2.4.66 or earlier with HTTP/2 enabled, including Azure Linux 3.0 and CBL Mariner 2.0 operators
| |
Patch within 24 hours.
Update httpd to a version newer than 2.4.66 using your distro's package manager (e.g., `tdnf update httpd` on Azure Linux), then restart the service.
|
NVD
MSRC
|
|
CVE-2026-43058
CVSS 7.1
EPSS 0.02%
|
HIGH
|
A kernel bug in the vidtv virtual DVB driver passes structs by value incorrectly, causing uninitialized memory reads flagged by MSAN. Exploitation requires local access and use of the vidtv test driver, which most production systems never load.
Affects: Azure Linux 3.0 operators running kernel 6.6.134.1-2 who have the vidtv module loaded (uncommon outside testing environments)
| |
Monitor and patch.
Update the kernel package to the patched version via `tdnf update kernel` on your next maintenance window.
|
NVD
MSRC
Ref 1
|
|
CVE-2026-44503
CVSS 7.0
|
HIGH
|
Kiota's built-in HTTP redirect handler forwards Cookie and Proxy-Authorization headers when it follows a redirect to a different host. If your app talks to an external API that issues a cross-host redirect, those credentials leak to the second server. Exploitation requires a redirect scenario, but that's easy for an attacker who controls or compromises the target API.
Affects: Developers using Microsoft Kiota client libraries in Java, .NET, Python, TypeScript, or Go
| |
Patch this week.
Upgrade your Kiota HTTP or abstractions package to the latest fixed version in your language's package manager (Maven, NuGet, pip, npm, or Go modules) and rebuild.
|
NVD
Ref 1
Ref 2
|
|
CVE-2026-42596
CVSS 9.4
|
CRITICAL
|
Gotenberg's downloadFrom and webhook features have a server-side request forgery (SSRF) bug that bypasses the default deny-list. An unauthenticated attacker can make your Gotenberg instance fetch internal URLs, potentially reaching cloud metadata endpoints, internal APIs, or other services behind your firewall. CVSS 9.4, so treat this seriously.
Affects: Anyone running Gotenberg v8 (the Go-based document conversion service), especially instances exposed to untrusted input or the internet
| |
Patch immediately.
Upgrade to the fixed version of Gotenberg v8 immediately and verify your deny-list configuration blocks internal/metadata endpoints.
|
NVD
Ref 1
Ref 2
|
|
Community Signal Check
|
PAN-OS User-ID Portal: Unauthenticated RCE Exploited in the Wild (CVE-2026-0300)
Unauthenticated root-level RCE in the PAN-OS User-ID Authentication Portal, already exploited in the wild and on CISA's KEV list. Patches start rolling out May 13. Until then, restrict portal access to trusted zones or disable it entirely if you run PA-Series or VM-Series firewalls with the portal exposed to the internet.
Palo Alto Networks
•
active_exploitation
|
|
Weaver E-cology 10.0 RCE (CVE-2026-22679) Exploited Since March
Attackers are hitting an unauthenticated RCE in Weaver E-cology 10.0 (CVSS 9.8) through an exposed debug endpoint. Exploitation started just 5 days after the vendor shipped a fix back in March, so unpatched instances have been wide open for months. If you run E-cology, patch immediately and check for signs of compromise.
The Hacker News
•
active_exploitation
|
|
Linux Kernel Privilege Escalation (CVE-2026-31431) Added to CISA KEV
CISA added this 9-year-old local privilege escalation bug to KEV on May 3 after confirmed exploitation in the wild. A 732-byte PoC gives unprivileged users root via a logic flaw in the kernel crypto template. Update to kernel 6.18.22, 6.19.12, or 7.0 if you haven't already.
The Hacker News
•
active_exploitation
|
|
|
That's your patch day digest.
|
|
patchdayalert.com
|
|
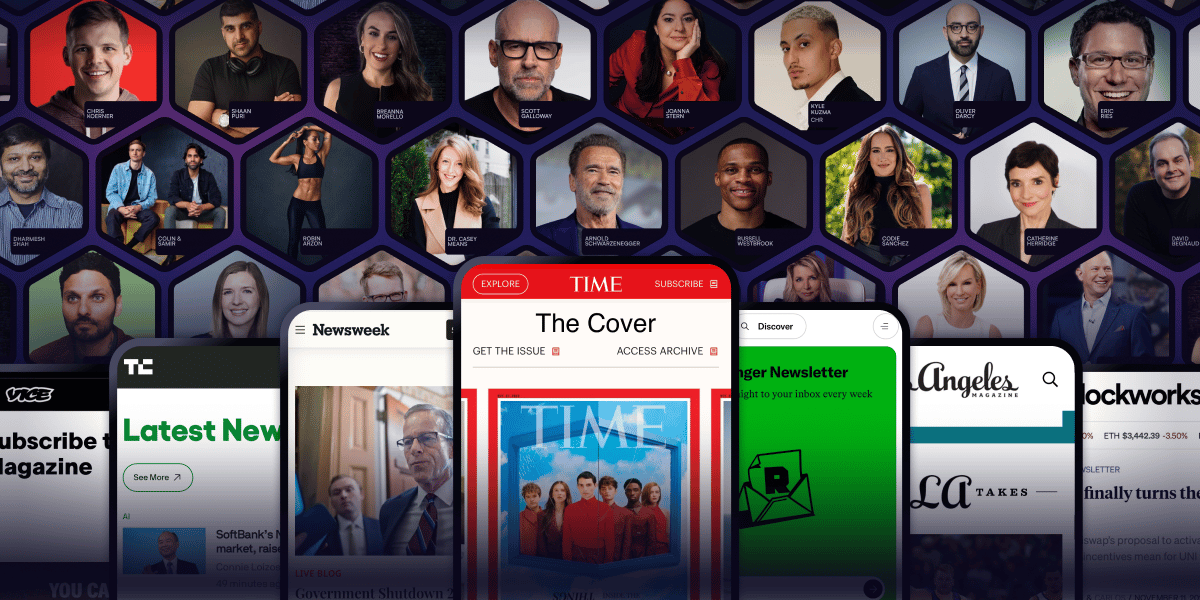
Arnold Schwarzenegger has a newsletter.
Yeah. That Arnold Schwarzenegger.
So do Codie Sanchez, Scott Galloway, Colin & Samir, Shaan Puri, and Jay Shetty. And none of them are doing it for fun. They're doing it because a list you own compounds in ways that social media never will.
beehiiv is where they built it. You can start yours for 30% off your first 3 months with code PLATFORM30. Start building today.