In partnership with

PatchDay Alert: 2026-05-04

|
|
DAILY BRIEF · MAY 4, 2026
|
|
Calm Monday, nothing on fire, but a few things worth your attention. Two GoBGP bugs (CVE-2026-7736, CVE-2026-7735) let unauthenticated peers crash your BGP daemon via malformed MRT or AIGP attributes. And if you run Prefect, MindsDB, or yudao-cloud: public exploits are already circulating for all three, with no vendor patches in sight for the last two.
|
|
TOP THREAT TODAY
|
|
An attacker can remotely trigger an integer underflow in GoBGP's MRT file parser (parseRibEntry), which could crash the BGP daemon or cause unpredictable behavior. No authentication is required. If you use GoBGP for route processing or MRT dump ingestion, this could take down your BGP sessions.
Who's affected: Network engineers running GoBGP 4.3.0 or earlier for BGP routing or MRT processing
| |
Patch this week.
Upgrade GoBGP to version 4.4.0.
|
NVD
Ref 1
Ref 2
|
|
|
CVE-2026-7735
CVSS 7.3
|
HIGH
|
An attacker can remotely send a crafted AIGP (Accumulated IGP) BGP attribute that triggers a buffer overflow in GoBGP's packet parser. This could crash the daemon or potentially allow code execution. No authentication is needed, so any peer, or anything spoofing a peer, could fire this off.
Affects: Network engineers running GoBGP 4.3.0 or earlier
| |
Patch this week.
Upgrade GoBGP to version 4.4.0.
|
NVD
Ref 1
Ref 2
|
|
CVE-2026-7723
CVSS 7.3
|
HIGH
|
Prefect's WebSocket endpoint at /api/events/in has no authentication. An attacker can connect remotely and inject events without credentials. A public exploit is already available, so expect scanning for this soon if it hasn't started already.
Affects: Teams running self-hosted PrefectHQ Prefect 3.6.13 or earlier with the API exposed to a network
| |
Patch within 24 hours.
Upgrade Prefect to version 3.6.14.
|
NVD
Ref 1
Ref 2
|
|
CVE-2026-7711
CVSS 7.3
|
HIGH
|
MindsDB's BYOM (Bring Your Own Model) engine handler lets a remote attacker upload arbitrary files through the proc_wrapper.py exec function with no restrictions. A public exploit exists, and the vendor has not responded to disclosure. There is no patch available right now.
Affects: Anyone running MindsDB version 26.01 or earlier, especially instances exposed to the network
| |
Patch immediately.
Restrict network access to your MindsDB instance immediately. Disable the BYOM handler if you don't need it. Monitor for a vendor patch, but don't hold your breath: the vendor has been unresponsive.
|
NVD
Ref 1
Ref 2
|
|
CVE-2026-7710
CVSS 7.3
|
HIGH
|
The JWT authentication filter in yudao-cloud (Ruoyi-Vue-Pro) can be bypassed by manipulating the mock-token parameter. An attacker can remotely authenticate as any user without valid credentials. A public exploit is available, and the vendor has not responded to disclosure. No patch exists.
Affects: Anyone running YunaiV yudao-cloud (Ruoyi-Vue-Pro) version 3.8.0 or earlier
| |
Patch immediately.
Take the application off the public internet immediately. Remove or hard-disable the mock-token functionality in JwtAuthenticationTokenFilter.java. No vendor patch is available, so you'll need to patch the code yourself or wait for a response that may never come.
|
NVD
Ref 1
Ref 2
|
|
Community Signal Check
|
cPanel zero-day CVE-2026-41940 auth bypass exploited by ransomware gangs
Attackers are exploiting CVE-2026-41940, a critical authentication bypass in cPanel/WHM, to get unauthenticated remote access to hosting panels. Ransomware operators have picked it up, and Shadowserver counts roughly 650K exposed cPanel instances online with 44K IPs actively scanning for the flaw. If you run cPanel, patch or restrict access to the management port right now.
Help Net Security
•
active_exploitation
|
|
Cisco SD-WAN zero-day CVE-2026-20127 exploited for 3+ years
Cisco Talos confirms CVE-2026-20127, an auth bypass in Catalyst SD-WAN Controller, has been exploited since at least 2023. Attackers use it to gain admin access, insert rogue peers into the SD-WAN management plane, and chain it with CVE-2022-20775 for further privilege escalation. If you run Catalyst SD-WAN, check for rogue peers and apply Cisco's fix immediately.
Cisco Talos
•
active_exploitation
|
|
Windows Shell CVE-2026-32202 exploited in the wild, leaks NTLMv2 hashes
CVE-2026-32202 is an incomplete fix for CVE-2026-21510 that lets attackers steal NTLMv2 hashes via zero-click SMB authentication. APT28 already weaponized the original bug, and exploitation is active in the wild now. If you haven't applied the latest April cumulative update, prioritize it, and consider blocking outbound SMB to untrusted networks as a backstop.
The Hacker News
•
active_exploitation
|
|
KB5083769 breaks RDP security prompts on multi-monitor setups
KB5083769 causes the RDP file security warning to render with overlapping text and hidden buttons on multi-monitor systems with mixed DPI scaling. You might not be able to click "Connect" at all. Microsoft says KB5083631 fixes it, so grab that update if your help desk is fielding complaints.
Microsoft Support
•
regression
|
|
|
That's your patch day digest.
|
|
patchdayalert.com
|
|
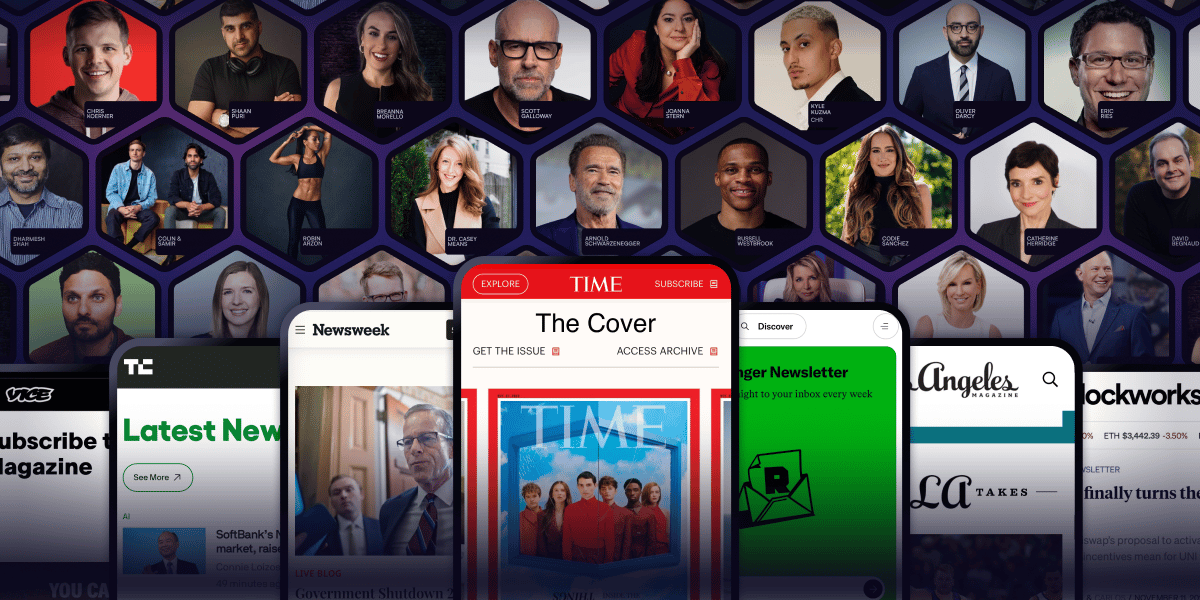
Arnold Schwarzenegger has a newsletter.
Yeah. That Arnold Schwarzenegger.
So do Codie Sanchez, Scott Galloway, Colin & Samir, Shaan Puri, and Jay Shetty. And none of them are doing it for fun. They're doing it because a list you own compounds in ways that social media never will.
beehiiv is where they built it. You can start yours for 30% off your first 3 months with code PLATFORM30. Start building today.