In partnership with

PatchDay Alert: 2026-05-05

|
|
DAILY BRIEF · MAY 5, 2026
|
|
Heads up: a CVSS 9.8 unauthenticated RCE in Linux's in-kernel SMB server (ksmbd) tops today's list. Nothing is exploited in the wild yet, but kernel-level remote code execution with no auth required doesn't stay quiet for long. Four more round out the day, including local privesc bugs in Norton Secure VPN and Amazon WorkSpaces plus a Node.js DoS via Axios.
|
|
TOP THREAT TODAY
|
|
An attacker can crash any Node.js service that passes user-supplied data through Axios's toFormData helper by sending deeply nested objects that trigger unbounded recursion. The server runs out of stack space and dies, giving you a straightforward denial-of-service. No authentication or special access is required if your API accepts arbitrary JSON bodies.
Who's affected: Node.js developers and DevOps teams running services that use the Axios HTTP library
| |
Patch this week.
Update the axios npm package to the latest patched version in every project that accepts external input, then redeploy.
|
NVD
Ref 1
Ref 2
|
|
|
CVE-2026-31705
CVSS 9.8
EPSS 0.05%
|
CRITICAL
|
ksmbd, the in-kernel SMB3 server in Linux, has an out-of-bounds write bug in its extended-attribute handling (smb2_get_ea). An attacker who can reach the SMB service could potentially get remote code execution at kernel level with no authentication. CVSS 9.8 says it all: if you expose ksmbd to any network, this is a top-priority fix.
Affects: Anyone running Azure Linux 3.0 with the ksmbd kernel module enabled, or any Linux host using ksmbd for SMB file sharing
| |
Patch immediately.
Update the kernel to a version newer than 6.6.134.1-2 on Azure Linux 3.0, or apply the upstream ksmbd patch for other distros. Disable ksmbd if you don't need in-kernel SMB.
|
NVD
MSRC
Ref 1
|
|
CVE-2026-37457
CVSS 7.5
EPSS 0.04%
|
HIGH
|
A vulnerability in FRR (Free Range Routing) affects Azure Linux 3.0 and CBL Mariner 2.0 packages. Details are sparse, but the CVSS 7.5 score and the affected product (a network routing daemon) suggest a remotely triggerable crash or information leak. If you run FRR on these platforms, treat this as a network-facing risk until more detail lands.
Affects: Teams running FRR on Azure Linux 3.0 (frr 10.5.0-2) or CBL Mariner 2.0 (frr 8.5.5-5)
| |
Patch this week.
Update the frr package to the latest available version on both Azure Linux 3.0 and CBL Mariner 2.0.
|
NVD
MSRC
|
|
CVE-2025-58074
CVSS 8.8
|
HIGH
|
During installation of Norton Secure VPN from the Microsoft Store, a low-privilege local user can swap out files in the install path. That lets them delete arbitrary files and escalate to higher privileges. This requires local access and the timing window of an active installation, so it's not remotely exploitable, but any shared workstation where Norton Secure VPN gets deployed is at risk.
Affects: Windows endpoint teams deploying Norton Secure VPN via the Microsoft Store, especially on shared or multi-user machines
| |
Patch this week.
Install the latest Norton Secure VPN update from the Microsoft Store and avoid deploying it on shared workstations until the fix is confirmed.
|
NVD
Ref 1
Ref 2
|
|
CVE-2026-7791
CVSS 7.8
|
HIGH
|
The Skylight Workspace Config Service in Amazon WorkSpaces for Windows has a flaw in its log rotation. A local non-admin user can plant arbitrary files in arbitrary locations, bypassing file system permissions, and escalate all the way to SYSTEM. You need local access, but no admin rights, so this is a real concern on any WorkSpaces desktop.
Affects: Teams running Amazon WorkSpaces for Windows with the Skylight Workspace Config Service older than version 2.6.2034.0
| |
Patch within 24 hours.
Update Amazon WorkSpaces for Windows to version 2.6.2034.0 or newer on all managed desktops.
|
NVD
Ref 1
|
|
Community Signal Check
|
April 2026 patches crash LSASS on domain controllers with PAM, causing reboot loops
April 2026 cumulative updates are crashing LSASS on Windows Server 2022 and 2025 domain controllers that have Privileged Access Management enabled. Affected DCs enter a reboot loop, which can take your whole domain offline. Microsoft already shipped out-of-band fixes, so grab those before you roll the April patches to any remaining DCs.
BleepingComputer
•
broken_patch
|
|
cPanel authentication bypass CVE-2026-41940 mass-exploited in 'Sorry' ransomware wave
Attackers are mass-exploiting CVE-2026-41940, a critical auth bypass in cPanel and WHM, to drop the 'Sorry' ransomware on web servers. Over 44,000 IPs running cPanel are reportedly compromised since late February. If you host anything on cPanel, patch immediately and audit for signs of unauthorized admin access.
BleepingComputer
•
active_exploitation
|
|
Linux kernel 'Copy Fail' CVE-2026-31431 exploited within 24 hours of PoC
CVE-2026-31431 (CVSS 7.8) is a local privilege escalation in the Linux kernel's AF_ALG crypto API. A public PoC dropped less than 24 hours before attackers started using it to get root on Ubuntu, RHEL, SUSE, Amazon Linux, and Debian, including container breakouts. Kernel updates are available across all major distros. Patch your Linux fleet now, especially anything running containers in the cloud.
Microsoft Security Blog
•
active_exploitation
|
|
Windows Shell CVE-2026-32202 exploited for NTLM relay, incomplete fix for earlier bug
CVE-2026-32202 (CVSS 4.3) is an incomplete fix for CVE-2026-21510. Even after April's patch, Explorer still leaks NTLM credentials to attacker-controlled servers when it renders a malicious LNK file. No user interaction required. APT28 and others are already exploiting this, so layer NTLM relay mitigations (SMB signing, restrict outbound NTLM) until Microsoft ships a complete fix.
Help Net Security
•
active_exploitation
|
|
|
That's your patch day digest.
|
|
patchdayalert.com
|
|
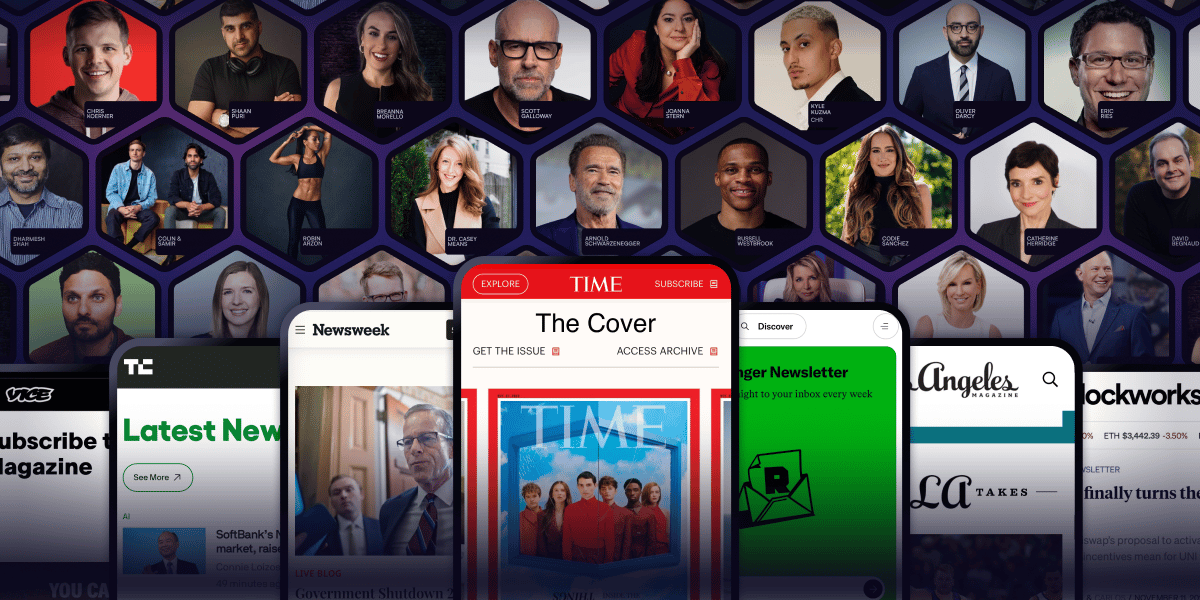
Arnold Schwarzenegger has a newsletter.
Yeah. That Arnold Schwarzenegger.
So do Codie Sanchez, Scott Galloway, Colin & Samir, Shaan Puri, and Jay Shetty. And none of them are doing it for fun. They're doing it because a list you own compounds in ways that social media never will.
beehiiv is where they built it. You can start yours for 30% off your first 3 months with code PLATFORM30. Start building today.